1. Analogy
- Uses information from past similar projects or the experience of team members to look for risks
- Previous projects must be up to date!
2. Brainstorming
- Brainstorming is a non-structured or semi-structured method of eliciting ideas from a group with the goal of generating a complete list of ideas
- The key to running a successful brainstorming session is to foster an atmosphere that allows all ideas to be spoken regardless of likelihood
- If everyone feels able to contribute to the discussion free from persecution or harassment a better more complete list of ideas will be generated
If not possible other techniques to brainstorming are available such as Delphi Technique or “Post-it Notes”
3. Delphi Technique
- Using this technique the participants are unknown to each other so ideas can be generated without fear of ridicule
- A moderator presents the question electronically to each participant who then generates ideas and sends them electronically to the moderator
- The moderator accumulates all responses into one list which is then distributed for team comment. The comments are returned to the moderator for accumulation and dissemination
- This process continues until a general consensus is reached.
4. Post-it Notes
- During a short time interval such as five minutes, have each participant write down on post-it notes as many ideas as they can think of putting one idea per post-it
- Participants then hand their notes to the moderators who stick them on a chalk or white board.
- A list of ideas is then quickly generated and the team discusses the merits of each
- Ideas which have close to zero probability of occurring or zero impact to the project are removed from the board
- The ideas that remain must then be rated for likelihood and impact. A large matrix is drawn on the board similar to the probability and impact matrix (Figure 8-2). The post-it notes can then be moved around inside the matrix until the team agrees on each placement
- Finally, generate the start of the risk register from the remaining post-it notes
5. Interviewing
- The project leader and other key members of the team with interview skills, conduct personal one-on-one discussions with key stakeholders
- The crucial aspect to successful interviewing is to make sure the stakeholders feel comfortable sharing ideas with the interviewer.
- The success of this technique is heavily dependent on the skills of the interviewer.
6. SWOT Analysis
SWOT is an acronym which stands for Strengths, Weaknesses, Opportunities, and Threats which was first defined and used during project selection in Chapter 4
SWOT analysis offers a framework with which to conduct a brainstorming session, sticky-note exercise, or a Delphi Technique session
A key benefit of this technique is a focus on both sides of each issue; strengths versus weaknesses and opportunities versus threats.
Strengths – patents, strong brand name, reputation, cost advantages from proprietary know-how, access to distribution networks
Weaknesses – lack of patent, weak brand name, poor reputation, lack of access to distribution networks
Opportunities – an unfilled customer need, arrival of new technologies, better regulations, international trade barriers
Threats – shifts in consumer tastes away from, substitute products, worse regulations, trade barriers
7. Cause-and-Effect Diagrams
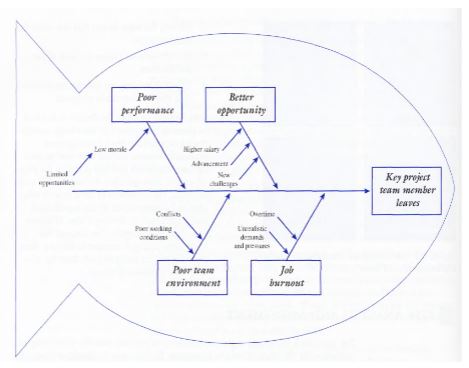
- The most widely known
and used cause-and-effect diagram is the fish bone, or Ishikawa, diagram developed by Kaoru Ishikawa to analyze the
causes of poor quality in manufacturing systems.
- The diagram can also be used for understanding the causes or factors of a particular risk, as well as its effects.
- An example of an Ishikawa diagram is illustrated above
- The diagram shows the possible causes and effects of a key member of the team leaving the project.
- This technique itself can be used individually or in groups by using the following steps:
(i). Identify the risk in terms of a threat or opportunity.
(ii). Identify the main factors that can cause the risk to occur.
(iii). Identify detailed factors for each of the main factors.
(iv). Continue refining the diagram until satisfied that the diagram is complete.
francis1897 answered the question on
March 14, 2023 at 11:07