Asynchronous transmission - data is sent and received one byte at a time. Used with
microcomputers and terminals with slow speeds.
Synchronous transmission — data is sent and received several bytes (blocks) at a time. It
requires a synchronized clock to enable transmission at timed intervals.
Kavungya answered the question on May 14, 2019 at 09:10
-
(i) Define the term "network firewall
(ii) Describe three advantages and three disadvantages of adopting hardware firewall.
(Solved)
(i) Define the term "network firewall
(ii) Describe three advantages and three disadvantages of adopting hardware firewall.
Date posted:
May 14, 2019
.
Answers (1)
-
Explain three modes of data communication and their practical use.
(Solved)
Explain three modes of data communication and their practical use.
Date posted:
May 14, 2019
.
Answers (1)
-
Explain four security concerns that personal computer users face in an organization.
(Solved)
Explain four security concerns that personal computer users face in an organization.
Date posted:
May 14, 2019
.
Answers (1)
-
List seven application packages of a computer system.
(Solved)
List seven application packages of a computer system.
Date posted:
May 14, 2019
.
Answers (1)
-
Briefly explain five features of a spreadsheet package.
(Solved)
Briefly explain five features of a spreadsheet package.
Date posted:
May 14, 2019
.
Answers (1)
-
Identify five types of file extensions.
(Solved)
Identify five types of file extensions.
Date posted:
May 13, 2019
.
Answers (1)
-
The following diagram gives an overview of computer software:
Required:
Identify two examples of each of the following computer software’s:
i. General purpose application programs.
ii. Application specific...
(Solved)
The following diagram gives an overview of computer software:
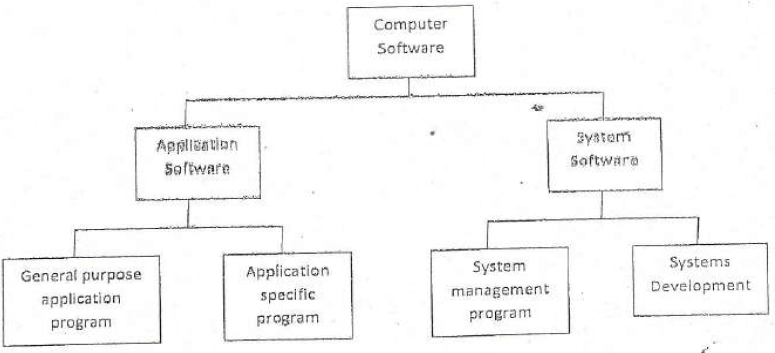
Required:
Identify two examples of each of the following computer software’s:
i. General purpose application programs.
ii. Application specific programs.
iii. System management programs.
iv. Systems development programs.
Date posted:
May 13, 2019
.
Answers (1)
-
(i) Briefly explain the term "machine level programming language".
(ii) State two advantages and three disadvantages of a machine level programming language.
(Solved)
(i) Briefly explain the term "machine level programming language".
(ii) State two advantages and three disadvantages of a machine level programming language.
Date posted:
May 13, 2019
.
Answers (1)
-
Discuss the factors that determine the processing power of a computer.
(Solved)
Discuss the factors that determine the processing power of a computer.
Date posted:
May 13, 2019
.
Answers (1)
-
Describe the following characteristics of computer "memory
i. Mutability
ii. Accessibility
iii. Addressability
iv. Volatility
(Solved)
Describe the following characteristics of computer "memory
i. Mutability
ii. Accessibility
iii. Addressability
iv. Volatility
Date posted:
May 13, 2019
.
Answers (1)
-
Describe four output devices that could be found in a television broadcasting station
(Solved)
Describe four output devices that could be found in a television broadcasting station
Date posted:
May 13, 2019
.
Answers (1)
-
Describe four characteristics of fifth generation computers.
(Solved)
Describe four characteristics of fifth generation computers.
Date posted:
May 13, 2019
.
Answers (1)
-
Briefly describe the concepts of downsizing as used in computer technology.
(Solved)
Briefly describe the concepts of downsizing as used in computer technology.
Date posted:
May 13, 2019
.
Answers (1)
-
Information communication technology (ICT) can be categorized into two broad
(Solved)
Information communication technology (ICT) can be categorized into two broad
products; traditional computer-based technologies and digital data communication
technologies.
Required
i. Using suitable examples highlight six traditional office applications of ICT.
ii. Briefly describe three specialized applications of ICT.
iii. Differentiate between "internal networks" and "external networks" as used in digital data
communication.
Date posted:
May 13, 2019
.
Answers (1)
-
(i) Briefly explain four approaches to computing in an organisation
(ii) Give one advantage and one disadvantage of each of the approaches explained in (b) (i)
above
(Solved)
(i) Briefly explain four approaches to computing in an organisation
(ii) Give one advantage and one disadvantage of each of the approaches explained in (b) (i)
above
Date posted:
May 13, 2019
.
Answers (1)
-
Demonstrate briefly how introduction of information technology could affect the following:
i. Products and services
ii. Production economics.
iii. Buyers.
iv. Suppliers.
v. Substitute products.
vi. Competitors.
(Solved)
Demonstrate briefly how introduction of information technology could affect the following:
i. Products and services
ii. Production economics.
iii. Buyers.
iv. Suppliers.
v. Substitute products.
vi. Competitors.
Date posted:
May 13, 2019
.
Answers (1)
-
Outline five methods of entering data into a computer system
(Solved)
Outline five methods of entering data into a computer system
Date posted:
May 13, 2019
.
Answers (1)